Personal identifiers of the future
Recent developments in the field of biometric security may dramatically affect the ways we make purchases, log on to computers, and even start our cars or unlock our doors. Biometric security systems can recognize an individual using a unique physical characteristic such as a fingerprint or facial image and may someday eliminate the need for PIN numbers and passwords. The use of body parts for identification is already a reality for many people when cashing checks or clocking into work.
Biometric security systems result from a marriage between established imaging technology and software that has evolved from machine vision and neural networks. The rapidly increasing power of PCs has reduced system costs and made the technology practical for a mass market.
That market is currently small but rapidly expanding. Sales data for biometric systems are difficult to come by, but annual sales probably total in the tens of millions of dollars for commercial applications. Annual growth may be as high as 50%, however. Michael Kuperstein, CEO of the face recognition firm Miros (Wellesley MA), says that sales for biometric applications including law enforcement and the military may reach $1 billion within the next five years. The largest potential market may be as an electronic signature for internet transactions. Home banking and similar transactions may eventually require greater security than PIN numbers or passwords can provide.
No identification system is perfect for all applications, however. There are two kinds of system inaccuracies—false acceptance and false rejection. The rate of false acceptance states the risk of validating unauthorized users, and the false rejection rate states the risk that the system fails to recognize a valid user. Different applications have different tolerances for these types of inaccuracy.
Accuracy and other factors have led to the development of systems that use different identifiers. Commercial systems are currently available that rely, for example, on fingerprints, iris patterns, facial features, infrared facial patterns, and hand geometry. Real and potential applications include making computers hacker-proof, providing ticket-less event entry, and eliminating welfare fraud. Fingerprint scans of orangutans are even helping naturalists track the endangered creatures in the wilds of Borneo.
Who needs this?
Losses from credit-card fraud are thought to exceed $1 billion each year, and theft of government medical benefits through fake identification (ID) is estimated at $6 billion a year. Clearly, relying on a picture ID to validate these transactions has proven inadequate.
There are two general types of applications for biometric security—identification and verification. The goal of identification is to find the name of an individual not initially recognized by the system. Verification, on the other hand, seeks to confirm the identity of a user who has previously registered with the system.
All biometric verification systems are based on a common concept. A user first must register with the system by having his or her biometric identifier scanned several times. The identifier is then digitized and encoded using a proprietary algorithm. When the user requests access, a new scan is taken and compared to the registration data. If a match is found, then the user’s identity is verified. The critical assumption is that the biometric scan is unchanging and unique to a particular individual. The prospect that biometric security will soon be commonplace is something to fear in the view of privacy advocates.
The public may feel that new applications compensate for a loss of privacy by bringing a measure of security to an insecure world. Applications under development include confirming a gun owner’s fingerprint before allowing the gun to be fired, verifying the identity of someone picking up a child from day care, and identifying newborns in the hospital.
Fingerprints
In the spring of 1997, 17-year-old Michelle Montoya was murdered in the woodshop of her Sacramento area high school. Her alleged killer is an ex-convict with a history of violence. At the time of Montoya’s death he was also a school employee.
In response to the Montoya murder the California legislature has made “live scan” fingerprint systems available to every school district. “Live scan” systems were developed in the 1980s to acquire and transmit forensic-quality fingerprint records for law enforcement. The first of the new systems, which cost $30,000 to $50,000, went on line this past July in the school district where Michelle Montoya had been a student.
The fingerprint scan is based on the ratios of ridges and valleys in the print. Problems arise, however, from variations in finger position and moisture, changes in skin texture, cuts, and so on. As a result, the rate of false rejects is relatively high. A much more serious problem however is public resistance to fingerprint scanning due to its connotations of criminal identification.
In fingerprint verification applications, this perception is somewhat unjust. Like other verification systems, it is the code that is stored, not the scans themselves. The fingerprints cannot be readily recreated, and matches are sought only with individuals who registered with the system.
Verification systems cost a great deal less than live-scan systems, particularly systems aimed at the PC market. A keyboard with a built-in fingerprint system is available from KeyTronic for less than $500. Compaq offers a simple fingerprint accessory that sells for $99.
The face is familiar
One technology with high public acceptance is face recognition. Low cost, familiarity, and ease of use make this the fastest-growing segment of the industry. With increasing numbers of video cameras appearing on PCs, face recognition hopes to tap into the market potential of validating internet transactions. Cost should not prove to be a barrier to the PC market. Miros’ TrueFace software can be downloaded from the company website for $59.95. Visionics (Metuchen, NJ) charges $300 for its FaceIt system, which includes a camera, frame grabber, and software.
Miros technology is already in use by the Mr. Payroll Corp. (Fort Worth, TX) at 35 of its check-cashing machines. It is estimated that one-third of adult Americans do not have a bank account, so reducing check-cashing fees by eliminating fraud could benefit a great many people. According to Miros and Mr. Payroll, their machines, which are similar to automatic teller machines (ATMs), have served more than 33,000 customers in the first nine months of service without a single improper transaction.
The Miros system uses neural network software, which records the characteristics of eyes, nose, chin, and so on in the context of the entire face. The system then recognizes the user “in much the same way as we recognize each other,” according to CEO Kuperstein, who states that neural networks have the ability to "learn" from additional input as to what is a good match and what is not.
The difficult part is distinguishing the face from the background of the image. Using a reasonably fast Pentium computer, the system defines the facial portion of the image typically in 2 to 3 seconds. Once this is done, the verification process itself takes a fraction of a second.
A significant advantage of face recognition over all other biometrics is that a user is easily recognized from his or her identifier. The system can keep a log of verification requests, that is, pictures of people who attempt to use the system. This feature alone might be sufficient to limit attempts at fraudulent access.
A warm smile
According to Technology Recognition Systems (TRS; Alexandria, VA), capturing facial images in the infrared (IR) eliminates the problems of low light levels and variations in appearance. TRS claims that the vascular system in the face produces a unique thermal pattern that does not change after adolescence. The uniqueness of this “thermogram” can distinguish between identical twins, even in the dark.
Thermograms record temperature ratios of facial regions; they are unaffected by changes in ambient temperature, because these ratios remain unchanged as the face warms or cools. The system ignores the patterns produced by the ears and nose, which are highly sensitive to ambient temperature changes. The image is even unaffected by cosmetic surgery.
In partnership with Unisys, Betac (Alexandria VA) a TRS subsidiary, is evaluating more than a dozen beta sites. Initially government installations are the primary market. With IR cameras alone typically priced at more than $10,000, cost is a major barrier for commercial applications. Betac states that component prices have been falling, however, and plans to reduce costs to make its systems more competitive.
Eyes that are the view
The most accurate biometric identifier is the pattern of an individual’s iris. The colored freckles, furrows, rings, and other features are formed in a random process during the first year after birth. The patterns are thought to be unique even between identical twins and to remain unchanged throughout life.
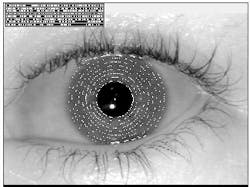
An iris scanning system photographs the iris, then digitizes and encodes the image (see figure). The rights to this technology are owned by IriScan (Mt. Laurel NJ), which calls the resulting encoded pattern an IrisCode. The company estimates that the probability that two irises could produce exactly the same IrisCode as approximately 1 in 1078.
Unlike the older retinal scanning technology—which maps the capillary pattern of the retina—iris scanning does not illuminate the interior of the eye. Dilation and contraction of the pupil in response to ambient light are compensated for in software by determining the inner and outer boundaries of the iris. The images are unaffected by glasses and contact lenses.
Spring Technologies (Falls Church, VA) is using IriScan technology in the development of its TranScan system, which is intended to eliminate tickets or tokens at subway and train stations on high-volume commuter lines. Sensar (Moorestown, NJ) has licensed the encoding technology from IriScan and is aggressively pursuing the ATM market. Sensar arranged a high-profile demonstration recently during which New Jersey governor, Christy Whitman, withdrew cash at an ATM using her iris scan for verification.
Iris scanning is also being considered for nonhuman applications, such as matching lab rats to their test results. OKI Electric Industry Co. Ltd. (Tokyo, Japan), and IriScan are jointly developing a system to guarantee racehorse identity. The Japanese Racing Association is hoping to use the system to identify approximately 10,000 thoroughbreds.
Business with a handshake
The Wall Street firm of Shearson Hamill (New York, NY) began using hand geometry measurement in the 1970s for access control. Hand geometry systems avoid the privacy concerns and the stigma of criminality sometimes attached to fingerprint scanning. The public seems to associate these systems with the simple act of shaking hands.
Hand geometry uses a video camera to measure the dimensions of an applicant’s hand, taking about 100 measurements of finger length, hand thickness, and so on. The HandKey system from Technology Recognition Systems, costing about $2500, is used in applications ranging from access control in nuclear power plants to identifying donors at sperm banks.
Advance and be recognized
Biometric security faces the same issues of standards and compatibility that confront all new technologies. Standards for cross-system data transfer and test criteria for comparing performance, along with safeguards for privacy, will go a long way to promoting the growth of the industry. But even if the marketplace accepts biometrics avidly, we will not be throwing away our keys and credit cards anytime soon.
Currently users must still present some identification, a card or password, to guide these systems in their database search. The biometric identifier is at present only a confirmation, just as a PIN is used to confirm an ATM account. As developers gain real-world applications experience however, and customers and the public gain trust in the technology, it seems possible that biometrics may become the only commercially accepted means by which we identify ourselves.
About the Author
Stephen J. Matthews
Contributing Editor
Stephen J. Matthews was a Contributing Editor for Laser Focus World.