Photonics promises improved security
While airport security has become an obvious priority since the September 11th attacks, relatively little change has been seen in the technology used to achieve higher levels of security. Now, though, several initiatives are emerging for development and introduction of new techniques based on optical technology that might help prevent future attacks on aircraft. Efforts are under way to use lasers to detect explosives, for holographic scanning to check for hidden weapons, and to implement already mature iris-scanning technology to help identify travelers and key personnel. Some of these measures raise serious privacy concerns, however, so it remains unclear whether passengers will, for instance, accept technology that allows them to be seen "naked" in exchange for a promise of safer skies.
Seeking explosives by laser
Explosives detection is one of the key objectives of airport security. This is a difficult task because explosives don't necessarily show up on x-rays. But work now being done by a joint project of The Federal Aviation Administration, Transport Canada, and IDS Intelligent Detection Systems (Nepean, Ontario) indicates that traces of explosives left on the outside of luggage can be detected by lasers.1
It is very difficult to avoid leaving microscopic traces of explosive on the outside of luggage if those handling the luggage have themselves packed the explosives. Conventional detection techniques, which involve wiping the luggage with solvent and then feeding the dissolved material through a gas chromatograph, are sensitive, but require that the luggage already be selected for further examination. Laser-based techniques could, in principle, scan all items of luggage. The IDS method looks for the light produced when tiny amounts of explosive are detonated by a laser pulse.
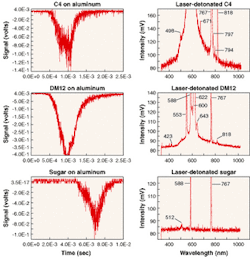
With a carbon dioxide (CO2) laser emitting at 10.6 µm, IDS researchers have shown that the pulse of light from the detonation of explosives can be detected considerably earlier than that from sugar, which was chosen as a typical nonexplosive combustible. Explosives such as PETN, RDX, and Semex-H detonated between 1 and 4 ms after the laser pulse started, while the light from the sugar peaked at 7 ms (see Fig. 1). For this application, long (millisecond) pulses were more effective than short (nanosecond) pulses, which ionized the explosive before it had time to detonate.
The spectra generated by the explosive detonations were also easy to identify and distinguish from that of sugar. The explosives all had a broadband peak with sharp lines due to elements like calcium and sodium. The sugar lacked the broadband peak altogether and had only a few sharp lines. While in the experiments, the laser beam was focused on a single 1-mm-wide spot, in an operational device the beam could be rapidly scanned over the whole surface of luggage, detecting nanogram-sized residues.
Millimeter-waves show hidden weapons
Laser inspection of luggage doesn't raise privacy issues, because luggage is x-rayed anyway and the laser only inspects the outside of the luggage. But privacy does become an issue with efforts to use millimeter-wave radiation, which penetrates clothing to search for concealed weapons.
Millimetric radiation (30 to 300 GHz) is generated by methods similar to those used at microwave frequencies but, because of to its short wavelength, can utilize technology like holography, which is based on optical techniques. For detecting weapons hidden on a person's body, the radiation has the dual advantage that it penetrates clothing easily but is reflected by metal, plastic, and just about any other material from which a weapon could be made. Scanners operating at about 100 GHz also exhibit high resolution, near 3 mm, which is adequate for detecting even small weapons and distinguishing them from innocuous objects like cell phones.
First-generation research versions of millimeter-wave scanners had significant limitations. A simple two-dimensional array of millimeter-wave detectors had relatively low resolution and could only image an area not much bigger than the millimeter-wave lens. Alternatively linear arrays of transmitter-receivers can quickly scan over the entire body. The image is formed using holographic techniques. Such systems, which operate at a single frequency, can produce a high-resolution image of the entire body but only at a single depth, since the depth of focus of the system is small.
Recent work by Battelle, Pacific Northwest National Laboratory (Richland, WA) has shown a way around this limitation by using a broadband, rather than a single-frequency source and an original algorithm to reconstruct a fully three-dimensional image with good depth-of-field.2 The algorithm is a combination of holographic techniques derived from optical holography and synthetic aperture radar techniques, which have been used to form images of terrain from aircraft.
In laboratory tests using 27- to 33-GHz radiation detailed images clearly show objects concealed under a volunteer's clothing. Commercial scanners would probably use a higher frequency range to give even higher resolution, around 3 mm. A new company, SafeView, (Richmond, WA) has been created to commercialize this technology.
The privacy concerns about millimeter-wave scanning are clear from the images produced. Since millimeter waves are reflected by the human body as well as by concealed objects, the scanned image shows the subject as naked (see Fig. 2). With 3-mm resolution, the view is about as detailed as one would get with ordinary vision of an unclothed person 15 ft away. It seems unlikely that airport passengers will put up with being seen naked by a stranger in return for enhanced security.
"The FAA has expressed concern about sending images of the person directly to an operator because of just these personal privacy issues" says Richard Rowe, CEO of SafeView. "These are valid concerns, and we have begun to address this issue by reprogramming the system to give the operator a view only of concealed items, not the person's whole body. We are still working on this." Allowing a computer to decide which parts of the image are body parts and which are concealed items, however, may involve putting too great a burden on pattern recognition software, especially if terrorists conceal weapons in curved-shaped containers. Whether passengers would have confidence in the software preserving their privacy is also an open question.
Iris scanning
Another technology that could improve security, but raises even more serious privacy concerns, is iris scanning (see photo). Iris-scanning technology from Iridian Technologies (Moorestown, NJ) for positive identification was introduced in October 2001 on a voluntary basis for frequent flyers at Schiphol Airport in Amsterdam, The Netherlands, and is now being extended on a mandatory basis to key airport and airline employees. EyeTicket (McLean, VA), which licenses the technology from Iridian, is providing iris-scanning machines for a trial at Heathrow Airport in London (see Laser Focus World, May 2002, p. 24)
As an identifying element, the human iris—the colored protein of the eye—has several advantages. It is an integral part of the body so is not amenable to easy modification. Also, unlike fingerprints, it can be imaged at a distance. Iris patterns are unique to individuals—even identical twins don't have identical patterns, nor does a person's right eye match the left eye. The patterns are stable throughout life and only change in a highly predicable manner as the pupil opens and closes in reaction to light.
The algorithm used in iris identification was developed beginning in 1980 by University of Cambridge computer scientist John Daugman and was first implemented in 1989. Since then, Daugman and his colleagues, ophthalmologists Aran Safir and Leonard Flom, have made substantial improvements to the technique, as more computer processing power became available, in the process forming IriScan, now available from Iridian.
The core of the system uses a mathematical technique called wavelet analysis to translate an image of the iris into a 512-byte pattern. Wavelet analysis is a mathematical relative of the more familiar Fourier analysis, and breaks down a pattern into a set of spatially limited waves. The pattern is defined in a coordinate system that is invariant both to the changes in pupil contraction and to the size of the image itself.
The initial commercial trial applications of iris scanning were as a substitute for passwords to identify customers at bank teller machines. Pilot projects at the Nationwide Building Society in England and the United Bank in Texas, however, were unsuccessful as the banks found the new technology too expensive.
In the wake of September 11th, emphasis has shifted to security applications, beginning with projects at Schiphol and London Heathrow airports. In the voluntary program at Schiphol, called the "Loyalty Program," citizens of European Union countries may apply for a pass that allows them to avoid both customs and immigration checks. Instead, travelers are cleared through the checks by looking into a machine that matches their iris pattern against a database of "Loyalty Program" members. The program also brings perks like free parking, but costs $90 and requires the applicant to submit to a background check, as well as to the iris scan. "In the first three months of operation at Schiphol about 2000 travelers signed up," says Linda Page, Iridian's director of marketing. Of course, a drawback of such a system is that it could itself be open to gross abuse if, for example, members of such a loyalty program started smuggling, knowing that they would not be subject to customs checks.
In the fall of this year, Schiphol expanded the iris identification program to a number of its employees who have access to aircraft, such as maintenance personnel. Mandatory iris scanning raises privacy concerns among civil rights experts, because it might be a step toward a universal identity card based on iris scanning. Schiphol tried to meet these concerns by not putting the iris scan data for its employees into a data bank. Instead, the employee carries a card with the iris scan on it. The scan code from the card is then compared with the person's own iris scan. In this way iris scan data could not be used for other purposes, such as beginning to compile a national identity data bank.
Such biometric-based national identity cards are a matter of debate in several countries, causing deep concern among civil rights advocates. "Perfect identity equates to perfect control" says Simon Davies, director of Privacy International, a Washington-based advocacy group. In the hands of authoritarian governments anywhere in the world, the ability to track citizens with perfect reliability could be a formidable mechanism of repression. Whether iris scanning is used for such purposes, or remains a part of mainly voluntary programs remains a matter for public policy debate. As with all security systems, methods of protecting security without violating the right to privacy will be a product of both technological development and the political process.